Seminar 人事・採用のセミナー
1~15件を表示
-
【WEBセミナー】オンライン面接対応 面接官トレーニング 基礎編
-
場所
オンラインセミナー (Zoom)
-
日程
2024.04.23(火) 10:00~12:30
2024.05.08(水) 10:00~12:30
2024.05.15(水) 10:00~12:30
2024.05.22(水) 10:00~12:30
2024.05.29(水) 10:00~12:30
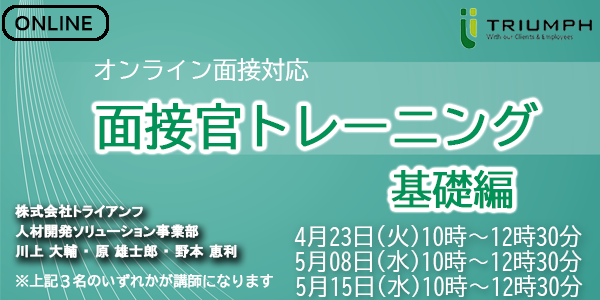
従来の面接官トレーニングの内容に、オンライン採用の考え方を加えバージョンアップ。
売り手市場を踏まえ、より一層対策が求められる面接という場において、
面接官がおさえておくべきポイントを、短時間で効率よく知ることができます。
模擬面接を行うことにより、講師から直接フィードバックを得ることも可能です。
「もうすぐ面接が始まる、その前にポイントを抑えておきたい」そんな方にも効果的です。
【POINT】
・「なぜ面接に対策が必要なのか」を理解できる。
・昨今の面接官に求められる役割について理解できる。
・応募者を見極めるための効果的な進め方、質問方法について理解できる。
・オンライン面接の注意点について理解できる。
・模擬面接を通じて「自分の癖」を知ることができる。 -
-
無料※録画配信※ 離職防止に使える!適性検査CUBIC活用セミナー
-
場所
オンラインセミナー (Zoom)
-
日程
2024.04.25(木) 14:00~15:00
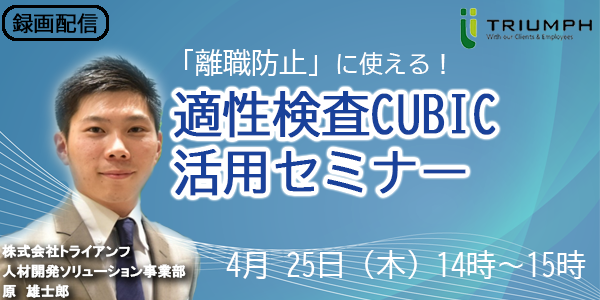
「離職防止」にも活用できる!適性検査の効果的な活用方法をご紹介するセミナーです。
多くの企業が、採用選考の参考資料として適性検査を利用しています。
本セミナーでは、 適性検査(CUBIC)の本来の使い方をお伝えすることで、適性検査を、採用・組織の「課題解決」に生かしていただくセミナーです。
面談時の志望度向上(動機付け)や、「早期離職」や「選考辞退」などの課題に、適性検査をどのように活用していくのかを、セミナーを通じてお伝えします。
【POINT】
・離職防止のための、適性検査(CUBIC)の活用方法がわかる。
・採用のみではなく、組織改善と連携した使い方がわかる。
※本セミナーは録画配信です。 -
-
無料※録画配信※ 採用すべき人物像を言語化・定量化!~新卒採用の基準設計セミナー~
-
場所
オンラインセミナー (Zoom)
-
日程
2024.05.09(木) 10:00~11:00
2024.05.30(木) 14:00~15:00
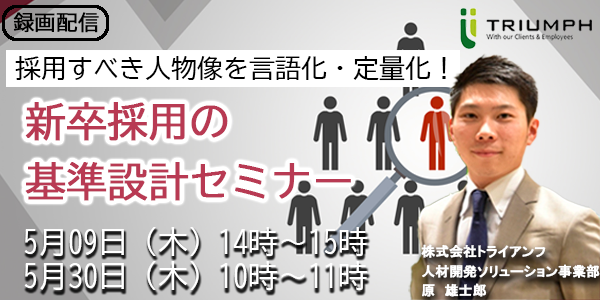
新卒採用の曖昧な求める人材像を言語化・定量化する方法と共に、
求める人材を惹きつける方法までお伝えさせて頂きます。
【POINT】
・採用基準設計の手順がわかる。
・採用基準に当てはまる人材への惹きつけ方法がわかる。
※本セミナーは録画配信です。 -
-
無料※録画配信※ 採用/組織課題可視化の第一歩 適性検査データ分析(基礎編)
-
場所
オンラインセミナー (Zoom)
-
日程
2024.05.16(木) 14:00~15:00
2024.05.21(火) 10:00~11:00
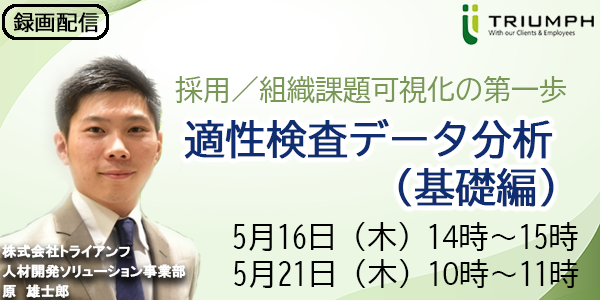
「採用/組織課題の可視化」というテーマを適性検査データ分析の観点から
知っておくべき基礎知識や、具体的な分析事例をお伝えします。
データ分析の専門知識がない方でもご参加いただけるセミナーです。
【POINT】
・自社に蓄積されたデータの活用方法がわかる
・他社の分析事例がわかる
※本セミナーは録画配信です。 -
-
【新入社員研修】新入社員立ち上がりセミナー~マインドセット編~
-
場所
オンラインセミナー (Zoom)

社会人として求められる【マインド・活躍するための考え方】を学べる新社会人向けのWEBセミナーです。
「自己認識力」という切り口でビジネスで活躍するために必要な考え方や行動をワークショップを通して学んでいきます。
【POINT】
・社会人として必要なマインド、活躍するための考え方を学べる
・不安、失敗への対処方法が学べる
・ワークショップを通して、自分の強み弱みを理解し、自己認識力を高めることができる。 -
-
【新入社員研修】新入社員立ち上がりセミナー~スキルセット編~
-
場所
オンラインセミナー (Zoom)

社会人として求められる【ビジネスマナー・ビジネスコミュニケーション方法】を学べる新社会人向けのWEBセミナーです。
「そんなこと知らなかった…」を防ぐために必要なマナーなどをワークショップを通して学んでいきます。
【POINT】
・社会人として必要なビジネスマナーを学べる
・ビジネスコミュニケーションのPDCAを学べる -
-
無料※録画配信※ 学生に寄り添う!内定者フォローセミナー
-
場所
オンラインセミナー (Zoom)
「いつ内定辞退が起こるかわからない」
このような不安を感じる企業様が年々増加しています。
昨今の採用は、内定を出したあとの施策が非常に重要視されており、
適切な内定者フォローが採用活動の成功・失敗を左右します。
本セミナーでは、学生の悩みをいち早く捉え、
内定者フォローの考え方や具体的な方法についてお話します。
【POINT】
・内定者の意識変化と、それからの悩みがわかる
・様々な内定者フォローの施策と他者事例がわかる
※本セミナーは録画配信です。 -
-
無料【CUBICリニューアル】分析機能解説セミナー
-
場所
オンラインセミナー (Zoom)
2024年1月にリリースするCUBIC新システムの「分析機能」に特化したセミナーとなります。
分析機能で何を確認できるのか、またどのように採用業務に活用できるのかなど、具体的な活
用方法を中心にご説明いたします。 -
-
無料【CUBICリニューアル】解説セミナー
-
場所
オンラインセミナー (Zoom)
2024年1月にリリースするCUBIC新システムについてのセミナーとなります。
実務をご担当頂く皆様が不安なくご利用頂けるように、旧システムと新システムで何が変更に
なったのか、追加されたのかを中心にご説明資料とデモ画面の両方をご覧いただきながらご説
明致します。
-
-
無料※録画配信※【モチベーションを上げ、自律的成長を促す】メンバーとのコミュニケーションの基本
-
場所
オンラインセミナー (Zoom)
「社員(部下)とのコミュニケーションの質を上げる」ということをテーマに置き、
準備すべきことや理解しておくべきこと、意識すべきこと等、
取り組んでいただいて決して損のない内容をお伝えします。
【POINT】
・社員、部下をフォローするうえで意識すべきポイントがわかる
・コミュニケーションの質を上げる具体的な手法がわかる
※本セミナーは録画配信です。 -
-
無料【新卒採用】2024卒総括&2025卒成功に向けたポイント解説セミナー
-
場所
オンラインセミナー (Zoom)
24新卒採用が収束に向かいつつ、既に25新卒採用活動が始まってきています。
各社の採用意欲は依然として高まり続けている現在において、
24卒採用の振り返りをご一緒させていただくなかで顕著となっている課題感や、
今後の採用に求められる動きなどを、ポイントをおさえながらお話します。
なかなか振り返りの時間が取れずお困りの方や、施策ご検討中の方はぜひご参加ください。
【POINT】
・24新卒の採用でみえた傾向
・25新卒採用戦略を立案、施策を実行するためのポイントや基本的な考え方
・選考中(内定)辞退やミスマッチ(早期離職、定着)に対する取り組み方のヒント
-
-
無料※録画配信※ 内定に繋がる、インターンシップ企画セミナー
-
場所
オンラインセミナー (Zoom)
選考早期化が益々進み、より注目されるようになっているインターンシップ。
大半の企業がインターンシップを実施する中で、悩みも増えてきているかと存じます。
実施しているが、思った通りにいっていない
企画しているが、説明会との違いが上手く作れない
実施した後、本選考まで繋ぎ止めることが難しい
3月以降のエントリー数が減る中で、
インターンシップは採用成功への生命線とも言えます。
そんなインターンシップを実施していく中で、今の企画にも活かせる、
学生が求めてる点や、実施後のフォローまでポイントを絞ってお伝えします。
【POINT】
・最新の新卒マーケットの状況が理解できる。
・学生が求めるインターンシップの内容と、企画の仕方が分かる。
・インターンシップ実施後のフォローの手法を知ることができる。
※本セミナーは録画配信です。 -
-
【WEBセミナー】面接官トレーニング 実践編(動機づけ編)
-
場所
オンラインセミナー (Zoom)
「応募者の入社意欲を醸成する」ために必要な姿勢、対応方法について
本番で使えるレベルまで落とし込むことを目的にした実践型のセミナーです。
動機づけを実施するために必要となる
「双方向のコミュニケーション」と「エピソードトーク」についてご説明します。
【POINT】
・昨今の応募者が何を求めているのかが理解できる。
・応募者に対して伝えるべき自社の魅力について整理することができる。
・入社意欲を醸成するために必要な「双方向のコミュニケーション」が理解できる。
・より効果的な「エピソードトーク」を準備するイメージが湧く。 -
-
無料メンバーのモチベーション向上を促す「タイプ理解」とは? ~成功する1on1~
-
場所
オンラインセミナー (Zoom)
本セミナーでは、メンバー育成にモチベーション向上がどれほど重要かをご紹介します。
また、コミュニケーションを円滑にする「個人のタイプ」を理解する方法もお伝えします。
心理的安全性の向上や、1on1ミーティングを成功に効果を発揮するなど、効果の高い方法を習得頂けるセミナーです。メンバーの育成に悩みのある方は、ぜひこのセミナーご参加ください。
【POINT】
・メンバーを理解することで、モチベーションを上げることができる。
・個人の特性を4つのタイプに分けて理解し、相手に合わせたコミュニケーションができる。 -
-
無料【開催終了】メンター・OJTの若手との関わり方 ~ソーシャルスタイルに合わせたコミュニケーション~
-
場所
オンラインセミナー (Zoom)

若手の定着促進、パフォーマンス向上のため、メンターOJT制度を導入されている企業様は多いかと存じます。
それでも「予想した効果が出ない」とご相談いただく声も多いのが実態です。
本セミナーは、今一度メンターOJTの役割、在り方を見直し、そのために準備すべきこと、本人たちが身に着けるべきスキルをご理解いただけます。
また、従来のOJTセミナーに「ソーシャルスタイル別アプローチ」の要素を加え、メンターOJT、新入社員の間で多様化する価値観を踏まえたコミュニケーションのポイントをお伝えします。 -




